ROYAL AIR FORCE CROUGHTON, England -- The digital world has become an important part of our lives. We pay bills, we stay connected with our friends and family, we shop. All of this adds up to vast amounts of data moving around the internet, leaving our personal and financial information vulnerable to cybercrimes. Phishing is an example of a highly effective form of cybercrime that enables criminals to deceive users and steal important data (Alkhalil, Z. (2021). The purpose of this article is to expose the reader to the many different forms of Phishing and how to better protect yourself from these attacks.
Phishers conduct their attacks by using psychological manipulation to scare or trick individuals into disclosing personal information. Much like the wide variety of predators lurking in the ocean, Phishing attacks come in in many forms. We will be sticking with the more common exploits people will see such as Phishing E-mails, Spoofed Websites, Phone phishing/Smishing, and social media attacks.
Email Phishing
The phishing emails are the most common of the listed attacks and follow the basic formula listed below:
1. The phisher sets up a fraudulent email containing a link or an attachment (planning phase).
2. The phisher executes the attack by sending a phishing email to the potential victim using an appropriate medium (attack conducting phase).
3. The link (if clicked) directs the user to a fraudulent website, or to download malware in case of clicking the attachment (interaction phase).
4. The malicious website prompts users to provide confidential information or credentials, which are then collected by the attacker and used for fraudulent activities. (Valuables acquisition phase). (Alkhalil, Z. (2021)
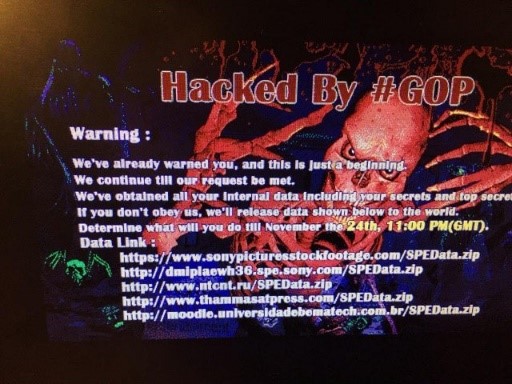
A good example is the email phishing attack that happened to Sony employees Nov. 24, 2014. These hackers posed as Sony employees and sent out a malicious link. This link was then passed around the company enabling the hackers to make off with hundreds of terabytes of company data, including movie files, financial records, and even customer data. Below is an image from the attack
Website spoofing
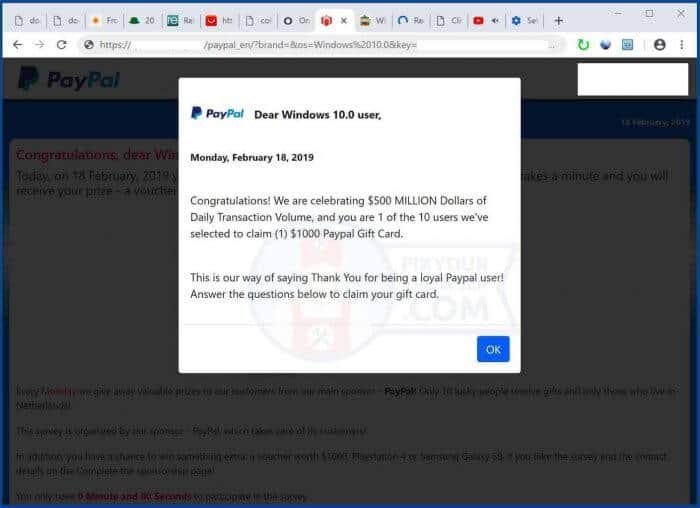
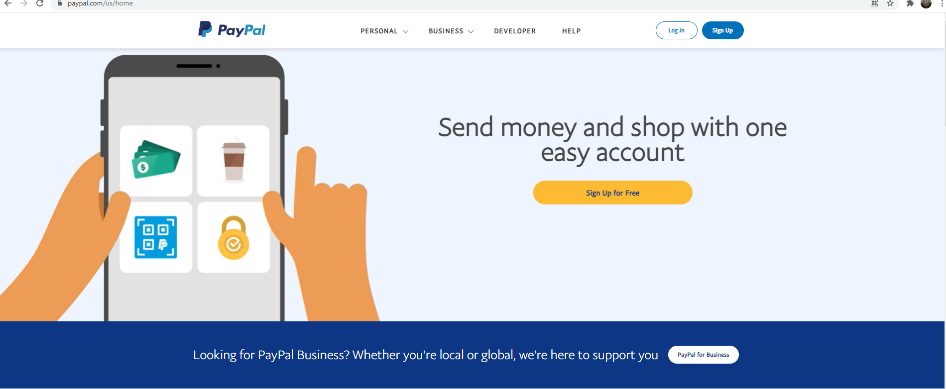
Website spoofing can be as simple as the following: pay.pal.com/us/home versus the actual website paypal.com/us/home. Did you catch the difference? Another difference to look for is the secure connection status, HTTPS vs the unsecure HTTP, next to the URL. These miniscule changes are what make it so easy to make mistakes, especially when we’re in a hurry. The longer users interact with the website, the more susceptible they become to disclosing personal data. The sites below are shots of the PayPal website and a spoofed website with a ludicrous pop up. Although most wouldn’t fall for such an obvious ploy, there are more subtle pop ups such as, “Please change your password.” or “Payment has been posted”. Two easy rules to for detecting a phishing are to ask yourself: “Did this try to get me to do something I wouldn’t normally do based on an emotional response?” and “Is this too good to be true?” If they are, use a different method to verify they are legitimate messages.
Phone games
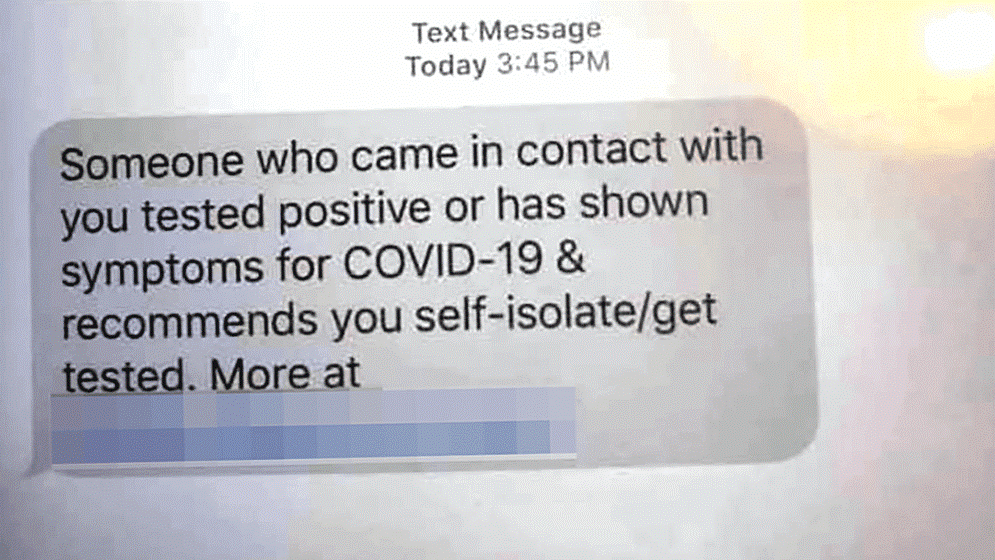
The last form of phishing, sometimes called Smishing, uses spoofed messages on your cell phone. This type of attack via messaging has becoming more prevalent, especially since COVID. Users are receiving convincing alert messages from their banks, healthcare providers and even shopping vendors which ask the victim to input their login credentials. Sometimes these links can also steal contact information, allowing the attacker to find further victims. Below are a couple of examples of Smishing texts that have been popping up the past couple of months.

What can we do
Phishing is something that will continue to happen as we become more reliant on technology. However, we can do our best to identify them and not fall for these sorts of attacks. The first thing is to be skeptical of unsolicited links. A little skepticism goes along way when it comes to unknown links. If it looks funny, ask questions and, especially if you are at work, report it. The next step is to have good antivirus which is up-to-date so you’ll have some backup, just in case you click that link that was sent to you via text or email. The antivirus software will help identify and stop malicious activity. The last thing we can do is use an anti-phishing toolbar extension. That’s an extension of antivirus that actively looks for phishing specific content and weeds it out.
Phishing remains one of the major threats to individual data today. Remember, phishing plays on our emotions and inattention so, don’t get sucked into the hackers’ trap. Keep calm and be skeptical.
References
Alkhalil, Z. (2021). Phishing Attacks: A Recent Comprehensive Study and a New Anatomy. Frontiers. https://www.frontiersin.org/articles/10.3389/fcomp.2021.563060/full#B98